Manufacturers are implementing technological advancements to enhance automation processes every day. We call this latest wave of rapid development Industry 4.0, the fourth industrial revolution. While modernization presents numerous opportunities for growth and process enhancement, experts are increasingly aware of their need for heightened security in an increasingly insecure digital landscape. Manufacturing and other industries are taking a closer look at cloud-based ERP and unified systems to address vulnerabilities.
IIoT Network Security Threats And How To Protect Operations
Over the last 10 years, system control integrators and industrial automation thought-leaders have sought to address what they’ve identified as the chief IIoT network security concerns. Manufacturing operations in the US and abroad have suffered a significant increase in disruption due to cyber threats and the trend appears to be steadily increasing. In 2013, of 257 total cybersecurity incidents, critical manufacturing comprised 15% of all attacks. That number rose by 12% in 2015, and another 6% to 33% of all incidents in 2015.

Manufacturing And Other Industries Are Taking A Closer Look At Cloud-Based ERP And Unified Systems To Address Vulnerabilities.
The proliferation of cyber-attacks, as evidenced in Triton, WannaCry, and Petya events, has left the executive suite on edge. According to a recent global survey, conducted as part of the Kroll Annual Global Fraud & Risk Report 2017/2018, 86% of executives put cybersecurity among their top anxieties, which the report refers to as a “new normal”. Seven in 10 of those surveyed in the manufacturing sector reported such an incident, either in the form of information/data theft, fraud, loss, or attack, has taken place within their operations over the last year. The report paid particular attention to organizations’ workforces, which routinely emerge as either paramount security assets or threats. This only highlights the importance of adopting comprehensive approaches to securing resources, equipment, and operational capabilities.
Cyber Arms Race: Cybersecurity IACS/IEC 62443-4-2 Certification
Among the reported incidents over the last 12 months, virus/worm infestations and email phishing scams topped the charts, at 36% and 33% of total incidents respectively. Examples of modern cyber threats, along with how they can be avoided, have been acknowledged by system integrators and cybersecurity professionals in a recent release of training resources from WoMaster, a networking and computing solution provider. Among the topics addressed are accidental unauthenticated access, common attacks experienced by system integrators, and intentional access by hackers who utilize specific skills and tools rank among the most critical concerns. Among these tools and skills are IP Source Guard, Dynamic ARP Inspection, DHCP Snooping, Denial of Service, and Distributed Denial Of Service exploits.

The Proliferation Of Cyber-Attacks, As Evidenced In Triton, Wannacry, And Petya Events, Have Left The Executive Suite On Edge.
The series seeks to educate critical manufacturing operators on the nuances of modern cybersecurity, the importance of adopting strict cybersecurity procedures, and conforming to the standards outlined in Cybersecurity IACS/IEC 62443-4-2 Certification. Such standards-based certifications offer economically efficient means of maintaining best practices when it comes to cybersecurity along with tangible benefits to operators and peace of mind for anyone whose data is stored in targeted digital systems.
How Cloud-based ERP Systems Address Security Expenses For SMEs
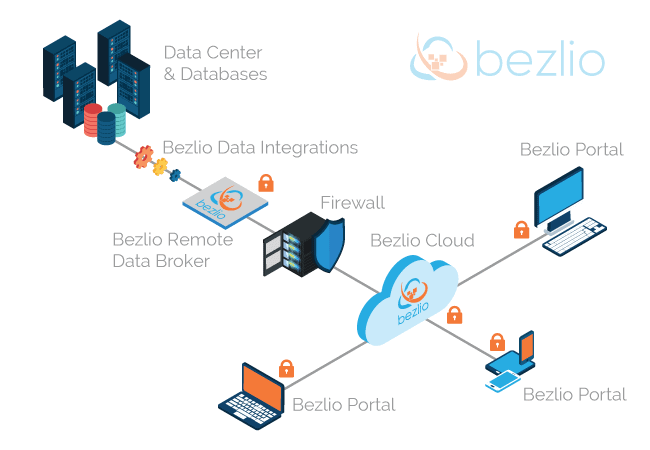
Cloud-based ERP systems are being relied upon by enterprises of every size more and more as time goes on. Cloud-based security is perhaps one of the biggest topics surrounding the efficacy of modern ERP systems.

SMEs Should Take Advantage Of This Highly-Secured Environment To Allow For More Focused Efforts On Growth.
Small and medium enterprises (SMEs), which may not have had much experience with cloud-based software, are typically the most skeptical. This is not to say that security risks don’t exist in the cloud. Security risks are always present. Handling security issues for cloud-based ERP is a challenging and complex process, not to mention costly. However, Cloud ERP providers, such as Epicor and NetSuite, spend hundreds of millions of dollars erecting formidable security apparatuses and maintaining and updating these safeguards regularly. That said, large, international manufacturers tend to keep their ERP systems on-premises, despite ERP providers offering high-level security for their cloud solutions. Solutions that SMEs are generally unable to implement themselves. As a result, it is advisable for SMEs to take advantage of this highly secured environment to allow for more focused efforts on growth. This way, SMEs can more readily compete in a marketplace where they are still considered the underdog.
About Encompass Solutions
Encompass Solutions is a business and software consulting firm that specializes in ERP systems, EDI, and Managed Services support for Manufacturers and Distributors. Serving small and medium-sized businesses since 2001, Encompass modernizes operations and automates processes for hundreds of customers across the globe. Whether undertaking full-scale implementation, integration, and renovation of existing systems, Encompass provides a specialized approach to every client’s needs. By identifying customer requirements and addressing them with the right solutions, we ensure our clients are equipped to match the pace of the Industry.